Why Concerns About A Trezor Hack are Overblown
Recently, the security team of Kraken Digital Asset Exchange published a hacking method to physically extract the word seed of the Trezor One and Trezor Model T hardware wallet.
This article explains why this hack does not significantly compromise the security of the Trezor devices, and how to mitigate this attack and similar ones. To read more about what the word seed is and how to secure it, read this article.
The hack requires physical access to the device and high technical skills
The hack disclosed by Kraken makes use of a voltage glitching technique. The hack requires that the Trezor device be taken apart. A hacker with sufficient electrical/computer engineering experience then needs to use several hundreds of dollars of specialized equipment to do a fault-injection attack, then brute force (try all possible combinations) of the pin number and finally extract the word seed.
The hack can be prevented by using the passphrase option
This entire hack can be fully prevented by using the Trezor passphrase option. If a user creates a long enough passphrase, the hacker will not be able to use this voltage glitching hack to brute force the device and obtain access to the word seed.
All hardware is hackable
There is no such thing as hardware that is immune to all physical hacks. The maxim“if you can get in, your enemy can get in” applies to information security justas much as the security of a building. Even if a computer hard drive is wiped, it is possible for digital forensic experts to extract the information from the hardware components.
Hardware wallets use secure microprocessors, but the private keys needs to be stored somewhere on the device, and there will always be some way that a skilled hacker with the right equipment can obtain them. The Keepkey hardware wallet also has a physical hack that was disclosed by Kraken recently, and a couple years ago, a 15 year old showed how he could break into the Ledger Nano S to extract the word seed.
All physical hacks can be prevented by securing your device
If hackers are not able to gain physical access to your hardware wallet, and you purchase your device from an authorized seller, then you can rest assured that you will not be the victim of a physical hack. If you are storing large amounts of cryptocurrency on your hardware wallet, you could leave it in a safe. You could then use another wallet, either hardware or software to store a smaller amount of funds and bring this with you when you travel.
Get free crypto investing & security guides, exclusive discounts, and more!
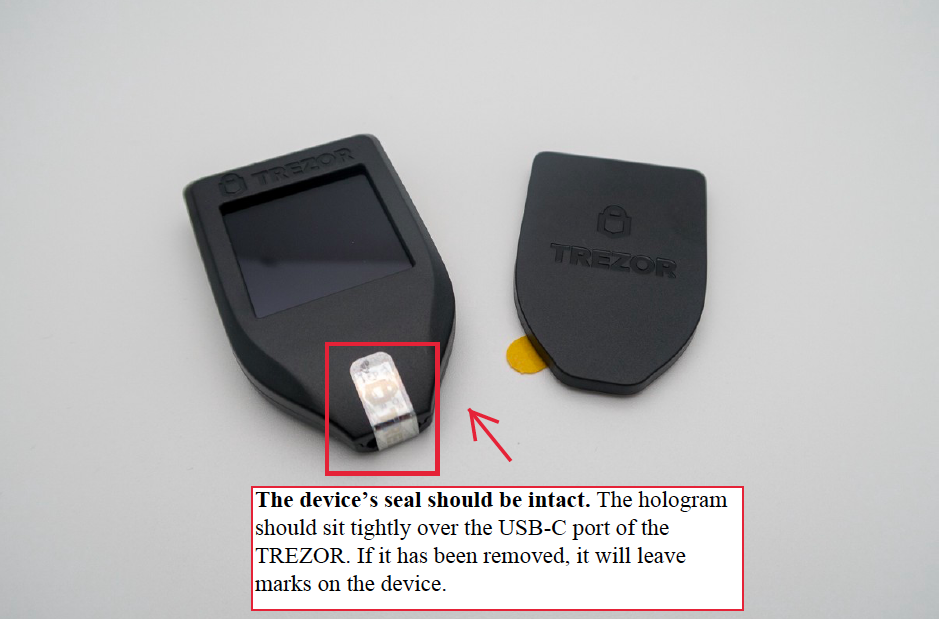
The other important security step is to make sure your Trezor wallet is secure to begin with. Always purchase the device from an authorized seller and check to make sure the tamper proof seal is intact and authentic. When you plug your Trezor in and download the firmware there is an additional software check that confirms the authenticity of the device.
You can get a backup wallet, in case of an emergency
Having a second Trezor wallet can help in an emergency where your device is lost or stolen and you need to quickly secure your cryptoassets before a hacker can gain access to your device. As soon as you realize that your device is missing, you can enter your recovery seed on your second device and gain access to all of your cryptoassets. You can then send all of your cryptoassets to a wallet with a new word seed. The word seed on the missing device will then have a zero balance, and even if a hacker were to extract it, there would be nothing they could do with it.
The odds are very low that if your Trezor device was lost or stolen, a hacker with the sufficient technical expertise and equipment could get their hands on your device, and obtain the word seed before you could send all of your crypto currencies to a new and safe word seed.
Remote attacks are the main threat in cryptocurrency
Hardware wallets remain the most secure cryptocurrency storage solution because remote attacks are far more common and easy to carry out. Exchanges offer poor security, as they are frequently the target of remote hacks and they do not even give you ownership of your word seed.
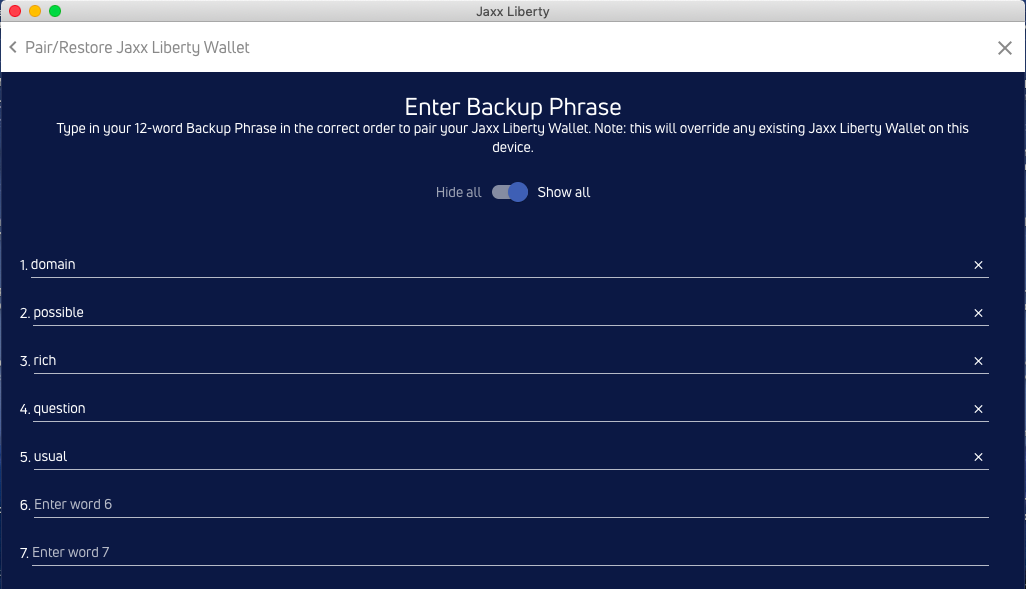
Desktop software wallets, while more secure than exchanges, still have vulnerabilities that hardware wallets do not have. These wallets require you to enter your word seed on a computer through a keyboard. Malware known as keyloggers can record keystrokes and hackers have now created these programs specifically to search for cryptocurrency word seeds.
Hardware wallets are not susceptible to this risk, as the word seed is entered only in the device.
Remote attacks such as malware, depend on the security of your computer and internet system which is never entirely in your control. Even if hardware wallets are plugged into an infected computer they remain completely immune to any malware. This is achieved by having the word seed and private keys stored on the hardware wallet’s microprocessor which remains isolated from the computer, even when plugged in.
Join the 10,000+ crypto investors & enthusiasts and get 10% off your first order.
Other steps to prevent hacks
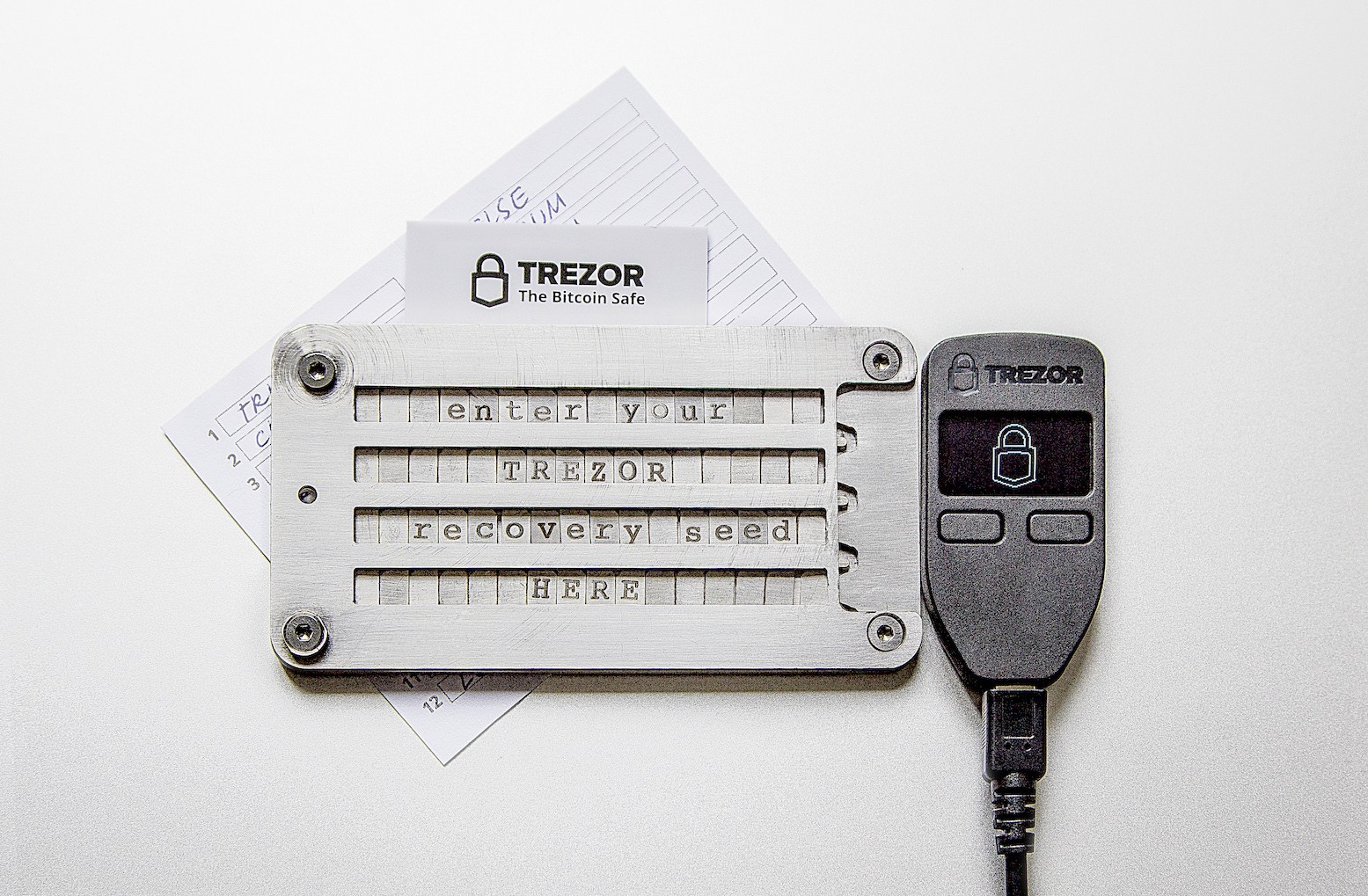
In addition to securing the physical Trezor device, it is crucial to secure the word seed. The word seed should only be recorded entirely offline, on paper or cryptosteel. This also means never taking a picture of your word seed with a mobile device or any other camera. When you first record your word seed, make sure every word, letter and the order of the words is correct. When you setup the Trezor device, also use the “check recovery seed” test to further confirm you copied down all the words accurately.
For additional security the word seed could be separated, and stored in two different secure locations. Remember though, that you should always have access to the word seed in case you get locked out of your device and you need to regain access to your assets.
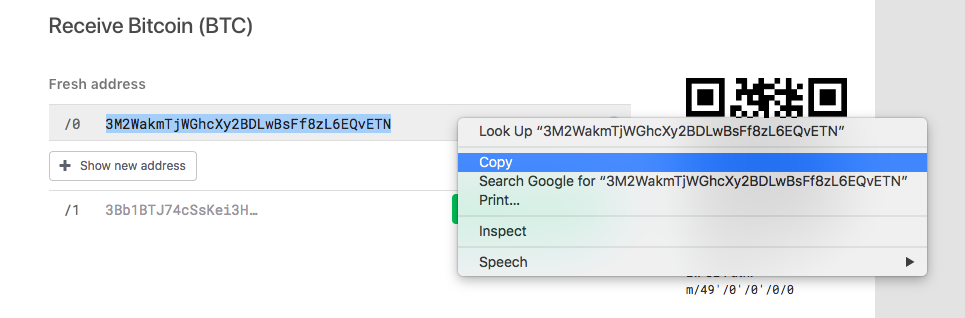
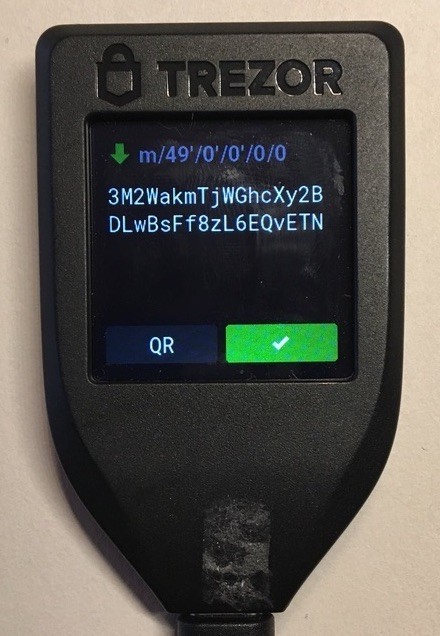
The only other method that a hacker could use against a user of a hardware wallet is a public key address attack. There are malware programs that display, via a popup screen, a fake public address on your computer screen right before you are about to make a transaction. If you send your coins to this hacker’s address, they will be lost. Fortunately, both the Trezor One and Trezor Model T, display the correct public address on the device itself. Before you send your cryptocurrency, always make sure the address on the Trezor device’s screen matches the address on the computer and you will be protected from this attack.
In summary, the steps that you need to take to make sure that your crypto assets are never stolen from your Trezor device or any other hardware wallet are:
- Purchase an authentic device from an authorized seller
- Protect your device from physical attacks (theft)
- Be ready to send your cryptoassets to a new word seed, in case of an emergency where your original word seed is compromised.
- Keep your word seed secure and entirely offline
- Confirm the public address on the device’s screen before you make a transaction.
Conclusion
Regard less of any physical attacks that hackers devise, hardware wallets are still by far the safest cryptocurrency storage solution. Hardware wallets are the only solution that give you enough autonomy to take the necessary steps that prevent all attacks. As long as you use your Trezor wallet effectively, one new hacking method will not be able to comprise your cryptoassets on the device.
JOIN NOW AND GET 10% OFF YOUR FIRST ORDER
Join the 10,000+ crypto investors & enthusiasts who receive exclusive discounts, crypto investing and security guides, digital privacy protection tips and more every week.